More SIM cards are vulnerable to Simjacker
Not long ago cybersecurity researchers reported a critical unpatched flaw in a wide range of SIM cards, which was actively exploited in the wild to remotely compromise targeted mobile phones just by sending a specially crafted SMS to them.
The Simjacker flaw resides in a dynamic SIM toolkit, called the S@T Browser, which comes installed on a variety of SIM cards, including eSIM, provided by mobile operators in at least 30 countries.
But now the security researchers discovered that the S@T Browser is not the only dynamic SIM toolkit that contains the Simjacker flaw.
It was found that another dynamic SIM toolkit, called Wireless Internet Browser (WIB), can also be exploited in the same way, exposing another set of hundreds of millions of mobile phone users to remote hackers.
For those who don’t know WIB toolkit is created and maintained by SmartTrust, one of the leading companies that offer SIM toolkit-based browsing solutions to more than 200 mobile operators worldwide, and, according to some press releases, the list includes AT&T, Claro, Etisalat, KPN, TMobile, Telenor, and Vodafone.
WIB toolkit has been designed to allow mobile carriers to provide some essential services, subscriptions, and value-added services over-the-air to their customers or change core network settings on their devices.
The flaw in S@T and WIB Browsers can be exploited by sending an SMS containing a specific type of spyware code.
The code can do the followings:
-Retrieving targeted device’ location and IMEI information,
-Sending fake messages on behalf of victims,
-Distributing malware by launching the victim’s phone browser and forcing it to open a malicious web page,
-Performing premium-rate scams by dialing premium-rate numbers,
-Spying on victims’ surroundings by instructing the device to call the hacker’s phone number,
-Performing denial of service attacks by disabling the SIM card, and
-Retrieving other information like language, radio type, battery level, etc.
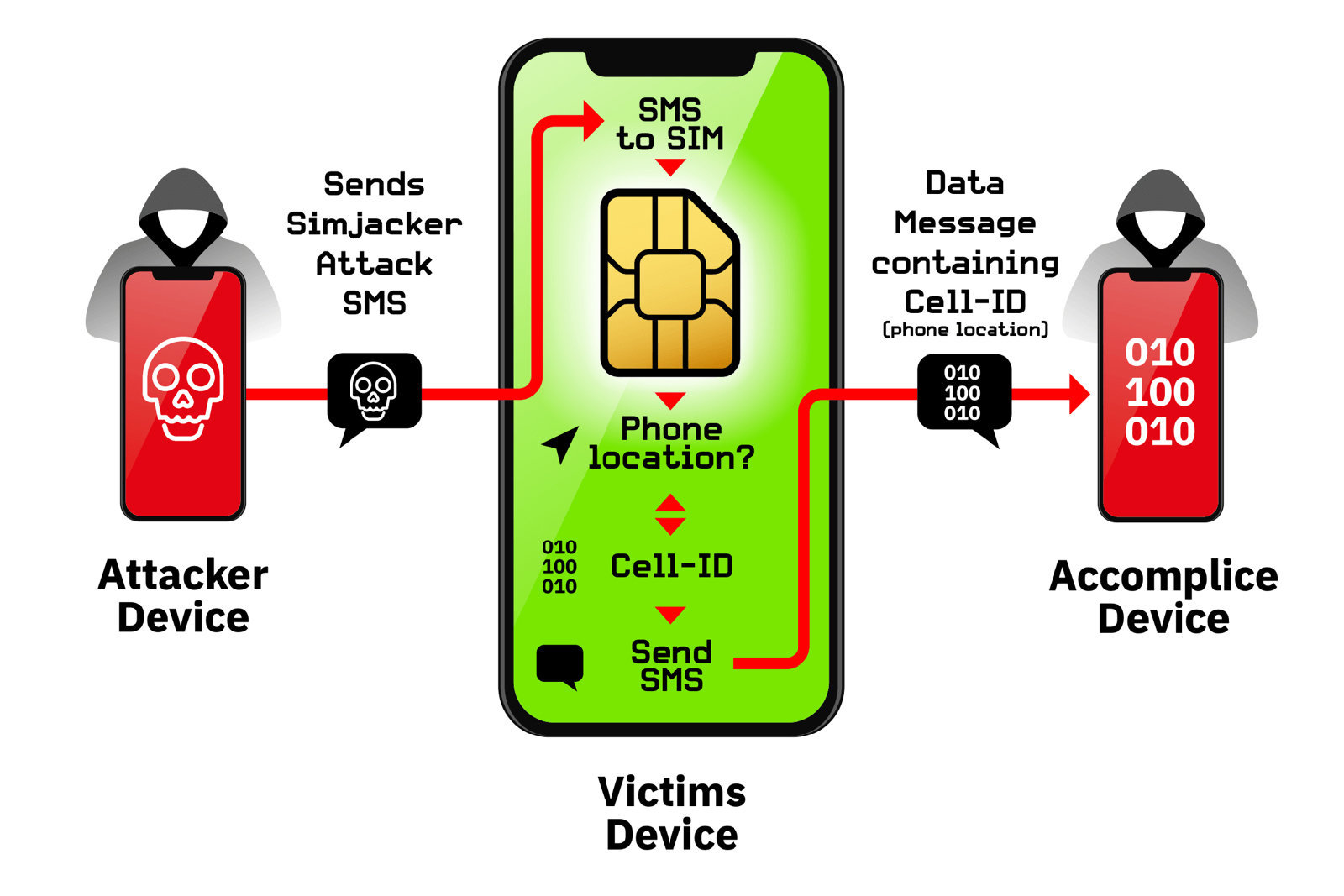
Both Simjacker and WIBattack attacks can be done in four easy steps:
-Hackers send a malicious OTA SMS to the victim’s phone number containing an S@T or WIB command such as SETUP CALL, SEND SMS, or PROVIDE LOCATION INFO.
-Once received, the victim’s mobile operating system forwards this command to the S@T or WIB browser installed on the SIM card, without raising an alert or indicating the user about the incoming message.
-The targeted browser then instructs the victim’s mobile operating system to follow the command.
-The victim’s mobile OS then performs the corresponding actions.
Security recommendation:
Researchers declared that they are working on a mobile phone app, to be released soon, which would allow users to scan their SIM cards to detect if it’s vulnerable to Simjacker vulnerability or not. But for the moment there is really not much a user can do to protect itself.